ISO 27032, the standard focused on cybersecurity

The International Organization for Standardization ISO created the 27032 standard focused on cybersecurity, taking into account that this is one of the greatest risks that companies face today.
This standard is intended to guarantee and ensure the security of information during exchanges, to avoid hacking, sabotage or alterations that could put it at risk.
Although there is ISO 27001 which is focused on information security, the International Organization for Standardization decided to create a principle focused on cybersecurity to give greater guarantees to organizations.
ISO 27032 offers the use of good practices in information security. In addition, it provides tools to manage it within an organization, it allows to have processes for the protection of operations and activities that are carried out online, the software used, data management, services, training the personnel who will be in charge. the handling of these tools.
"Cyberspace is a complex environment consisting of interactions between people, software and services for the global distribution of information and communication." It is a very large context in which "collaboration is essential to ensure a safe environment," said the ISO when presenting this standard.
This regulation was created with two purposes: to cover cybersecurity aspects that had not been touched in previous versions and to promote cooperation between agents such as CSF, CyberSecurity Framework and Cybersecurity Framework.
On the other hand, it is focused on four axes:
1. Information security.
2. Network security.
3. Internet security.
4. Protection of critical infrastructures for information.
What includes?
- Technologies in which it can be implemented.
- Security tools.
- Good practices.
- Policies.
- Security of digital assets.
- Training.
- Risk management.
- Security concepts.
- Guides and standards.
Objectives
- Offer security to the entire cyberspace of the company.
- Have a plan of action in case a crisis occurs.
- Plan the resolution of incidents.
- Provide training to members of the organization in everything related to cybersecurity and its risks.
- Create alerts to identify any threat that could endanger the assets of the company.
- Have a strategy to combat the risks that may arise or that will materialize.
- Identify the risks that may arise in this regard.
Controls
Applications
- Validation, codes and cookies.
- Sessions, scripts, policies and authentication.
- Persons
- Safety campaign.
- Constant training.
Servers
- Peches, backups, monitoring, testing.
- Installation and configuration standards.
Users
- Continuous training, personal IPS and firewall.
- Post office, web security and antivirus.
Recommendations
- Continuous training for the entire organization so that they are attentive and know how to act in case of an eventuality.
- Follow the good practices of ISO 27032.
- Review and monitoring of the implemented strategy to verify if the controls that are being carried out are efficient.
- Have a data and information protection program.
You May Also Like
These Related Stories

Classification and management of information assets

Unraveling Information Security Management Complexities

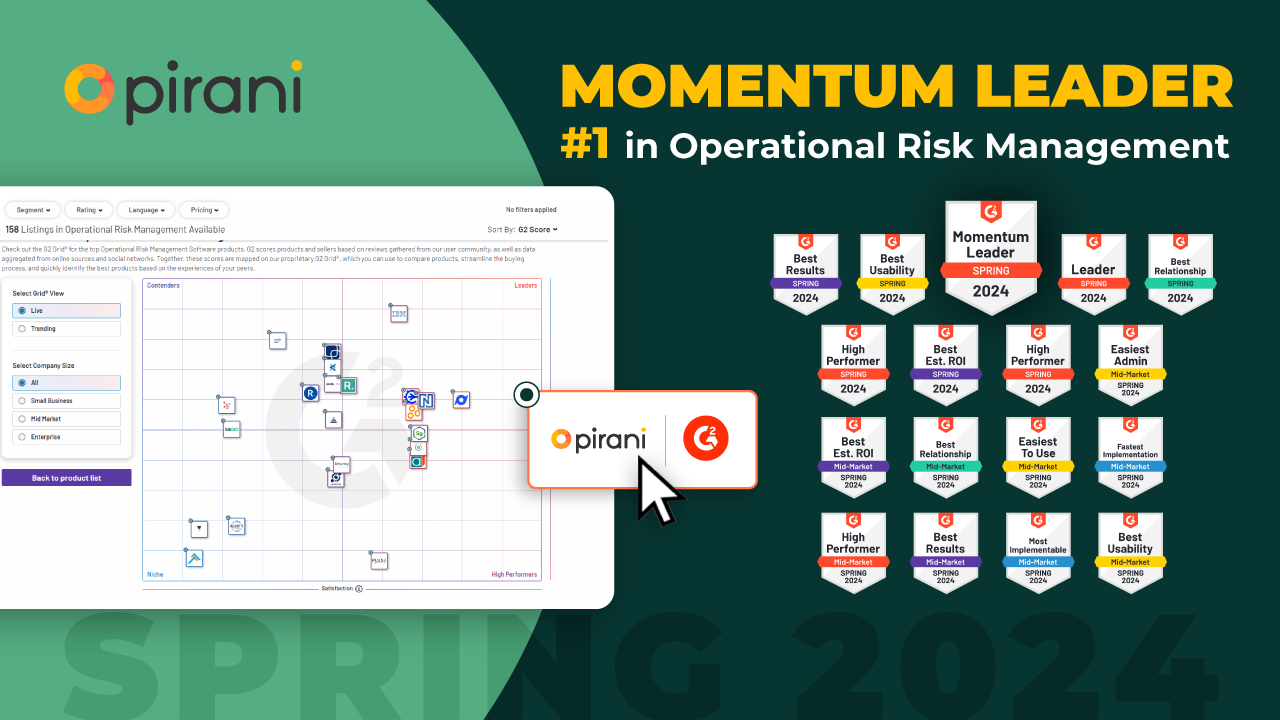
Pirani remains the leader in the operational risk Grid at G2

ISO 31000 Simplified: Elevate Your Risk Strategy

Why do banks retain inactive customer data?

No Comments Yet
Let us know what you think