Guidance for Compliance with New Money Laundering and Terrorist Financing
Introduction
The prevention of money laundering and the financing of terrorism are critical issues in the financial and corporate sphere in the United States. The Financial Action Task Force (FATF) intergovernmental organization has established international standards to combat these crimes and promote financial transparency. In this context, the United States has adopted new regulations in line with FATF recommendations to prevent and combat illicit activities.
In this guide, we will address the importance of compliance with the regulations on preventing money laundering and terrorist financing in the United States and provide some key recommendations for companies to comply. In addition, we will address the importance of employee compliance training and awareness and the consequences that companies may face in the event of non-compliance.
We will also share practical guidance for you to ensure compliance with regulations, including identifying and verifying the identity of customers, monitoring transactions for suspicious activity, and the measures necessary to safeguard the privacy and protection of customer data. In addition, how companies can demonstrate compliance with regulatory authorities and customers is discussed.
Finally, future trends and prospects in preventing money laundering and terrorist financing in the United States will be discussed. All of the information we share is extremely valuable to companies operating in the United States and those looking to expand their operations in the United States to ensure regulatory compliance and prevent illicit activities.
Money laundering and terrorist financing prevention regulations
New regulations introduced in the U.S. in line with FATF recommendations.
In January 2021, the U.S. Treasury Department issued new rules with the Financial Action Task Force (FATF) recommendations to combat money laundering and terrorist financing effectively. These regulations include the beneficial ownership rule (RBR) and FinCEN's Customer Identification and Identity Verification Rule.
The Beneficial Ownership Rule (RBR) stipulates that firms must identify and verify the identity of the beneficial owners of any legal entity wishing to open an account in the United States. Such a rule applies to all legal entities created in the United States or abroad and intended to do business in the United States.
On the other hand, FinCEN's Customer Identification and Identity Verification Rule requires financial institutions to verify the identity of their customers and perform a money laundering risk assessment on each of their transactions. In addition, the rule stipulates that financial institutions must maintain records and file suspicious transaction reports with the U.S. Treasury Department's Financial Crimes Enforcement Network (FinCEN).
Impact of the new regulations on companies operating in the U.S.
The new regulations significantly impact businesses operating within the United States, especially financial institutions and companies that open bank accounts or conduct financial transactions in the United States.
Therefore, financial institutions must implement additional compliance due diligence measures to verify the identity of customers and assess the risk of money laundering. Similarly, companies that open bank accounts in the United States must provide additional information about their beneficial owners and comply with all suspicious transaction reporting requirements.
In addition, companies that fail to comply with the new regulations may face significant financial penalties, fines, and reputational damage.
Practical guidance to ensure regulatory compliance.
Identifying and verifying the identity of customers
Companies should implement appropriate due diligence measures to identify and verify the identity of customers properly. This includes obtaining basic identification information such as name, address, and identification number and verifying the information using reliable documents and databases.
In addition, establishing clear policies and procedures for the identification and verification of customer identity, as well as for the periodic updating and review of customer identification information, is of utmost importance.
Monitoring transactions to detect suspicious activity.
Firms should implement appropriate measures to monitor transactions and detect suspicious activity that may indicate money laundering or terrorist financing. This may include reviewing transaction patterns, identifying unusual or complex transactions, reviewing transactions conducted by high-risk customers, and reporting suspicious activity to the relevant authorities.
Ensuring compliance with new regulations
Companies should implement additional compliance measures to ensure compliance with new regulations, including training staff on the rules, reviewing and updating existing compliance policies and procedures, and appointing a responsible compliance officer dedicated to overseeing compliance with the regulations.
It is also crucial that the company establish clear policies and procedures to ensure compliance with new regulations and incorporate regulatory changes into existing compliance programs.
Measures to ensure the privacy and protection of customer data.
The Financial Action Task Force (FATF) stipulates a series of recommendations to ensure the confidentiality and safety of customer data about money laundering and terrorist financing issues. Below, we mention some of these recommendations that companies should apply.

Proper collection and Use of Customer Data
Firms should collect only the information necessary to meet their legal and compliance obligations and use that data only for the purpose for which it was collected. In addition, effective procedures such as encryption and protection against unauthorized access must be followed to protect customer data adequately.
The process that can be followed to comply with this measure is as follows:
- Identification of the information needed to meet the company's legal and compliance obligations.
- Establishment of the policies and procedures necessary to collect and use customer data.
- Establishment of security measures necessary to protect customer data, such as encryption and protection against unauthorized access.
- Professional training of staff on privacy and data protection policies and procedures.
Informed Consent
Companies need to obtain customers' informed consent before collecting, using, or sharing their data to comply with this measure. That is why it is so important that customers' support is explicit, free, specific, and informed and that they have the option to withdraw their consent at any time.
The process to be followed to ensure compliance with this measure can be as follows:
- Establish a clear privacy and data protection policy that allows for customer data collection, use, storage, and protection.
- Seek informed consent from customers before collecting, using, or sharing customers' personal data.
- Ensure customer consent is explicit, freely given, specific and informed.
- Give customers the option to withdraw their consent at any time they wish to do so.
Restricted access to customer data
Companies should allow access to customer data only to those employees who need this information to perform their jobs. In addition, appropriate security measures should be implemented to protect customer data, such as using strong passwords and encryption of sensitive data.
The process to follow to achieve compliance with this measure can be as follows:
- Identify employees who need access to customer data to perform their jobs.
- Implement appropriate security measures to protect customer data, such as using strong passwords and encryption of sensitive data.
- Establish specific policies and procedures to allow access to customer data.
- Train employees on privacy and data protection policies and procedures.
Monitoring and tracking of customer data
To ensure compliance with this measure, companies must monitor and track customer data in detail to detect any misuse or suspicious use of data, such as in reviewing access logs and data usage patterns.
Comply with this measure requires following a process, which is as follows:
- Establish appropriate policies and procedures to monitor and track customer data.
- Monitor and track customer data to detect any improper or suspicious use of that information on time.
- Review in detail all access logs and data usage patterns.
- Train company personnel on privacy and data protection policies and procedures.
Staff training
To comply with this measure, the company's staff must be fully trained on privacy and data protection policies and procedures and applicable laws and regulations. All of this can help prevent errors and security breaches that could jeopardize the confidentiality of customer data.
The process to follow to comply with this measure consists of several steps:
- Identify applicable customer privacy and data protection laws and regulations.
- Establish effective policies and procedures to ensure customer privacy and data protection.
- Train company personnel on privacy and data protection policies and procedures.
- Provide regular training to keep staff updated on privacy and data protection policies and regulations.
Risk assessment
To achieve compliance with this measure, companies should conduct periodic risk assessments to identify potential threats to customer privacy and data protection. This can help identify areas for improvement and take proactive steps to protect customer data effectively.
The process to be followed to comply with this measure is as follows:
- Identify the types of data being collected and stored and the risks associated with each type of data.
- Assess the security and privacy risks associated with collecting and storing customer data.
- Identify existing security and privacy measures and determine what improvements can be made.
- Implement additional security and privacy measures to mitigate identified risks significantly.
- Conduct periodic assessments to ensure adequate identification and mitigation of risks.
To ensure customer data privacy and protection, companies should implement adequate security measures, obtain informed consent from customers, restrict access to customer data, monitor and track customer data, train staff, and conduct risk assessments periodically. This ensures that the protection of customer data is used responsibly and ethically.
Training and awareness of your employees for regulatory compliance.
Above, we mentioned the different regulations that prevent and sanction money laundering from illicit acts and terrorism through business organizations. Both facts have a social cost, preventing the continuity of honest organizations, and an economical price. According to the FBI, the deadliest terrorist attack in the United States cost almost $400,000.
Therefore, beyond rigid rules that impose severe fines and sanctions on companies, the regulatory authorities put the accent for prevention on the knowledge and understanding of the team members about the reason for the rule and the relevance of its compliance.
Relevance of having a trained and aware staff to comply with regulations.
Undoubtedly the importance of training and awareness of the members of the organization in all areas and levels on anti-money laundering and terrorism regulations is vital to ensure that they have the ability and expertise to identify irregularities in the activities and prevent money laundering from taking place.
This practical training can only happen through the implementation of a comprehensive program that allows members to know within their internal processes which are the main vulnerable areas; however, generic training is not enough; it must be adapted to the functions of each area, and it must be updated as new regulations and forms of money laundering or terrorist financing arise. Only in this way will companies be able to consolidate the culture of compliance and prevention to protect their financial stability and, more importantly, their reputation.
Let's look at how practical staff training should take place.
Employee compliance training and awareness program.
- Create a comprehensive AML and terrorist financing compliance program: This should describe with precision and extreme clarity all policies, procedures, and control measures necessary to detect irregularities (know what and where to look for) and prevent these activities.
- Identify risk areas: each organization must be able to detect those areas of greatest vulnerability, where there is a greater probability of money laundering or terrorist financing irregularities, for example, finance. Special attention must be paid to the methodology for incorporating new clients, monitoring transactions, and immediate notification of suspicious activity.
- Effective Training: in this step, the organization must design and adapt compliance training according to the roles and responsibilities of each area. In the case of employees who are part of the process of incorporating new customers, they will need more preparation in the evaluation of the profile of prospects and KYC requirements; however, those employees in the area of finance or administrative training will focus on segmenting the critical factors of each transaction to detect sudden or suspicious changes in patterns of behavior.
- Regular updating: the information provided to employees should be updated as new AML and terrorist financing protocols emerge; this ensures that they are updated with the latest regulatory requirements and best practices.
- Compliance culture: The key to consolidating it is to encourage continuous communication on issues related to these facts so that members of the organization can ask questions or express their concerns or worries. It can include rewarding those members who demonstrate commitment and collaborate with the prevention of money laundering and terrorism.
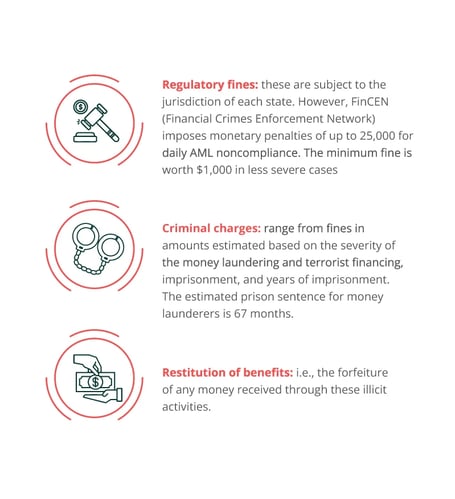
Noncompliance legal consequences for companies
Main penalties that companies may face if they do not comply with regulations.
There are different ways in which the regulations penalize noncompliance, depending on the seriousness and the state in which the event occurs. However, the penalties that they could face are:
8 ways to demonstrate compliance to regulators and customers
Demonstrating to authorities and customers that you are fully compliant with AML and terrorist financing regulations is vital to ensure the growth and viability of companies. Here are the best ways to achieve this:
- Develop a compliance program: as mentioned above, it is vital that companies implement an action plan that clearly and simply outlines their policies, procedures, and control methodologies to prevent money laundering and terrorist financing.
- Automated risk assessment: business organizations must implement an effective and automated risk management framework through systematic analysis of their activities to identify those areas of work most exposed to potential hazards that are conducive to illicit acts. To be a practical demonstration method, it is necessary that the assessments are documented and can be presented to the authorities at any time.
- Create training programs for personnel: They must understand the applicable regulations, why they must comply with them, and the negative impact it would have on the organization and them if they choose to ignore them.
- Training should focus on helping them be aware of the risks in performing their duties, quickly identifying suspicious activities, and providing them with the means to report them immediately.
- Suspicious activity alerts: An excellent way to demonstrate to authorities and customers the organization's commitment to preventing these crimes is to implement effective communication methods for employees to report suspicious activity. In addition, they should establish procedures for investigating and following up on these alerts. Also, it is best to inform the competent authorities that you have had a warning regarding a customer or a transaction that does not meet expected standards and is, therefore, under analysis. e.g., The international bank HSBC failed to keep proper records as part of its AML protocols and was fined $85 million for neglecting to file suspicious activity reports (SARs).
- External audits: In addition to the internal audits performed by the risk management team, companies must engage the services of specialized and independent organizations that can accurately and objectively assess whether the company complies with regulatory requirements. As recommended in the previous section, it is prudent to make the external audit results available to the regulators to ensure transparency in the activities.
- Multiple methods of customer verification: Business organizations should implement a strict customer onboarding process to ensure that their transactions include individuals and entities not involved in illicit activities. They must verify the legitimacy of identity documents, source of funds, and occupation and evaluate whether the income corresponds to the amounts handled in their operations.
- Transparency: this must be the protagonist in compliance programs, risk management, and audits and be able to make the necessary information available to clients and authorities.
Trends and prospects for preventing money laundering and terrorist financing in the U.S.
The AML market is estimated to reach 1.77 billion USD by 2023. In light of this increase in the incidence of cases, here are some current trends in the prevention of these crimes in the Americas that will continue soon:
Increased support in technology: technological solutions are expected to develop a more relevant role in preventing illicit activities; the use of AI and machine learning could be the key to quickly detecting suspicious patrons in a large volume of financial data.
Cooperation between institutions: government agencies and business organizations will work closely together to share relevant information and essential resources in the fight against money laundering and terrorism. It includes the creation of specialized groups and joint investigative activities.
Increased focus on cybersecurity: According to Getastra alone, in 2023, 8,00,000 cyber attacks have been recorded in total; this increase in cybercrime and the rise of cryptocurrencies, it is expected that government agencies and businesses should focus their focus on crime prevention in these unexplored areas that lack clear regulations. From identity verification methods that back up funds, monitoring and alerting on unusual behavior, even setting transaction limits, and keeping reliable and up-to-date records of transactions, etc.
Stricter rules: regulations and prevention protocols are likely to be deepened, especially in such novel areas as cryptocurrency transactions, tokens, etc., which are loopholes. The new policies will require companies to have a higher level of transparency and increase criminal and civil liability for their omission.
Pirani can help you make it happen!
Risk management technology solutions such as Pirani can play a crucial role in your company's compliance in the fight against money laundering and terrorist financing, as it is a tool that adapts and configures itself according to the rules and protocols that the organization must follow in each of its areas. It helps you to create regulatory compliance modules, set risks and is even capable of measuring the impact that the risk would have on your company.
In addition, it allows users to enter risk indicators to monitor in real-time the execution of activities and issue quick alerts in case of detecting irregularities or vulnerabilities. Pirani's risk management software also allows you to centralize all the information about your customers and operations, facilitates the management of internal audits, and issues reports on your company's current situation so that you can make the necessary changes.
See Pirani in action!
Conclusions
Every year, approximately $800 billion, which is nearly 5% of the world's GDP, is estimated to be laundered, making it difficult for honest businesses to break into the marketplace as they offer products and services at a meager cost. In addition, it allows criminal organizations to continue operating, so governments demand that businesses focus on regulatory compliance to prevent these illicit acts and ultimately ensure the continuity of legitimate companies.
To do so, they must demonstrate to government authorities and their customers their commitment and respect for the fight against these criminal activities. Their compliance actions should include the following:
- Implementing a comprehensive compliance program.
- Conducting regular risk assessments.
- Training personnel.
- Creating reliable channels for suspicious patterns.
They must also invest time and resources in external audits and applying KYC processes that provide transparency in operations.
Finally, current trends reveal that in the future scenario, in terms of regulatory compliance to combat money laundering and terrorism, technological solutions will play a leading role, which will be vital to dismantle the new ways of carrying out these crimes in the digital world, in addition, future regulations will favor interagency cooperation, to implement more robust compliance methodologies that can adapt as how these criminal acts are carried out evolve.
Bibliographic references
- Grupo de Acción Financiera Internacional (GAFI) - https://www.fatf-gafi.org/about/
- Grupo de Acción Financiera Internacional (GAFI) - https://www.fatf-gafi.org/countries/e-k/unitedstates/
- "Treasury Issues Final Rule on Corporate Transparency Act and Anti-Money Laundering" https://home.treasury.gov/news/press-releases/jy0003
- "Fact Sheet: FinCEN Takes Historic Action to Enhance Corporate Transparency" https://www.fincen.gov/news/news-releases/fincen-issues-final-rule-beneficial-ownership-reporting-support-law-enforcement
- "Estate and letting agency business guidance for money laundering supervision" https://www.gov.uk/government/publications/money-laundering-regulations-2007-supervision-of-estate-agency-businesses
- "Experience effortless collaboration and workflow efficiencies with HighQ" https://legal.thomsonreuters.com/en/products/highq
- "DAC 6: UK implementation of the new EU tax disclosure rules" https://www.nortonrosefulbright.com/en/knowledge/publications/c72547af/dac-6-uk-implementation-of-the-new-eu-tax-disclosure-rules-consultation
- "Guidelines to Notice 626 on Prevention of Money Laundering and Countering the Financing of Terrorism – Banks" https://www.mas.gov.sg/regulation/guidelines/guidelines-to-notice-626-on-prevention-of-money-laundering-and-cft-for-banks


